Edit: The original data for RDP in March, 2020 included IPv6 results whereas the historical analysis only looked at IPv4. I've changed the numbers to reflect the new counts. Tl;dr: we're still seeing growth but significantly less than before.
More companies are going remote due to COVID-19 and as a result there's been a lot of speculation around how this impacts the exposure of companies and the Internet as a whole (in terms of publicly-accessible services). I was actually already working on creating trends for various services due to a presentation I gave late last year so let me share with you some updated charts on how the Internet has evolved over the past few years (up to March 29, 2020).
Methodology
Just quickly I'll mention a bit about how the data itself is generated:
- Shodan infrastructure is globally distributed to prevent being geographically biased
- Crawlers run 24/7 and don't do sweeps of IP ranges the same way a network scanner would
- Crawlers attempt full protocol-specific handshakes to validate that a port is responding. Depending on the protocol Shodan also performs additional steps to validate the response. For example, in the case of RDP the crawlers grab a screenshot, perform OCR on that screenshot and do a variety of basic security checks.
Timeframe
Shodan keeps a full history of every IP in the Internet that it's ever seen. We store that archive in a variety of formats and for this purpose I reprocessed our data going back to the beginning of 2017. You can also access that historical data via the API, CLI, or the new beta website.
Aggregation
I binned the results by unique IPs per month for each port/ tag. This means that data is not based on point-in-time scans but rather an aggregate view of the active IPs during a month.
Remote Desktop
The Remote Desktop Protocol (RDP) is a common way for Windows users to remotely manage their workstation or server. However, it has a history of security issues and generally shouldn't be publicly accessible without any other protections (ex. firewall whitelist, 2FA).
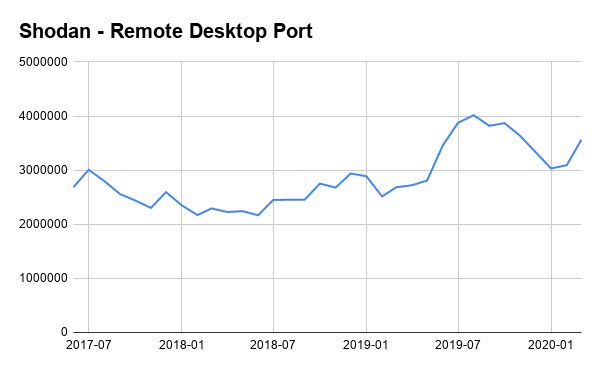
The number of devices exposing RDP to the Internet has grown over the past month which makes sense given how many organizations are moving to remote work.
It's surprising how the number of RDP instances actually went up after the initial Microsoft bulletin on Bluekeep in May 2019. And then it dropped sharply in August once a series of issues were revealed (DejaBlue) that impacted newer versions of RDP.
A common tactic we've seen in the past by IT departments is to put an insecure service on a non-standard port (aka security by obscurity). To that point, this is how the exposure for RDP looks like on an alternate port (3388) that we've seen organizations use:
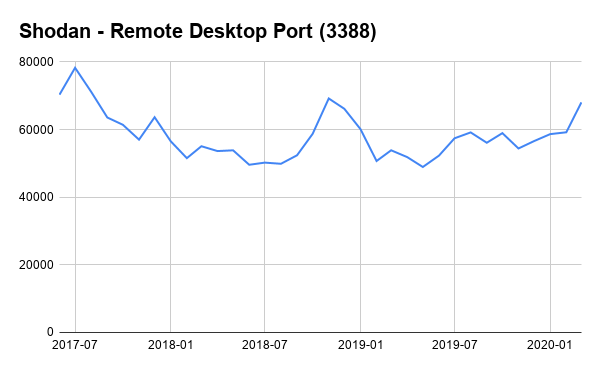
It follows very similar growth as seen for the standard port (3389). The last thing I wanted to point out is that 8% of the results remain vulnerable to BlueKeep (CVE-2019-0708).
VPNs
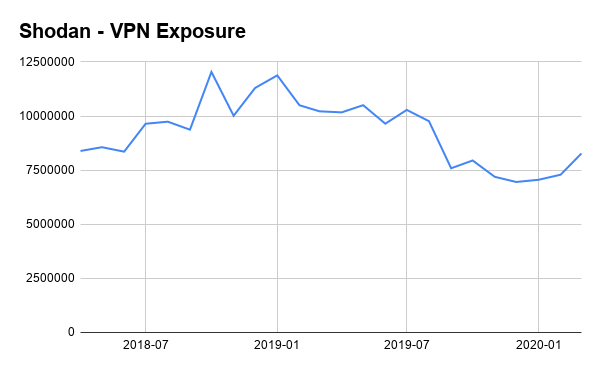
The above chart encompasses a few different VPN protocols and ports (IKE, PPTP etc.). VPNs are a secure way to allow remote workers access to your network and it's not surprising to see that number grow as well the past month.
Industrial Control Systems
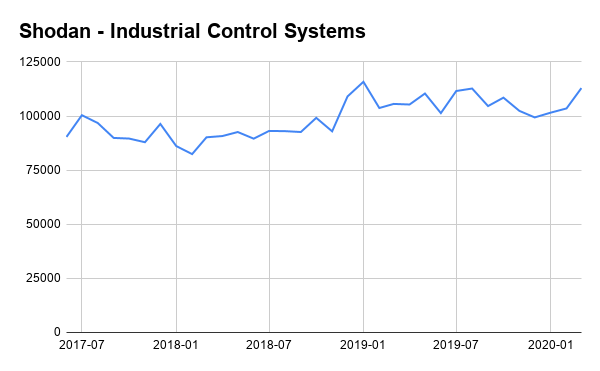
We've observed significant growth in other protocols (HTTPS) but one of the important areas where we've seen a worrying increase in exposure is for industrial control systems (ICS). The growth is not as large as for other protocols but these are ICS protocols that don't have any authentication or security measures. We had actually seen a stagnation in the ICS exposure up until now. And there have been significant advancements in OT security so there are plenty of secure options to choose from.
We're also keeping our country-wide exposure dashboards up-to-date if you'd like to see breakdowns by country.
Conclusion
I hope the above data provides a more data-driven view of how the exposure of those ports has changed the past few years. There aren't any earth-shattering surprises in the data but it's good to validate what many already assumed. If you're an organization that is concerned with your Internet exposure and wants to keep track of what you have connected to the Internet then please check out our Shodan Monitor service.